Resources
Understanding Role Delegations in Oracle ERP/HCM Cloud
Fraud and Data Loss - one and the same?
Securing the Financial Close
It's time we started approaching Internal Controls and Data Security as the same discipline.
According to IBM’s “2020 Cost of a Data Breach Study,” the average total cost of a data breach rose from $3.62 million to $3.86 million, an increase of 6.4% over the previous year. Understandably, the study found, the longer it takes to identify and contain a breach, the greater the cost.
We must also look at the Association of Certified Fraud Examiners Report to the Nations for 2020, where we find that a typical fraud case lasts 14 months. On average 5% of revenue is lost through fraud each year, and areas such as asset misappropriation & financial statement fraud schemes accounting for some of the most frequent and most costly losses.
Just as data losses are often discovered by a third party (data being sold on the dark web for example) so too fraud is uncovered usually by a third party.
So, are Fraud and Data Loss the same? Technically not, and yet the consequences of both are becoming more aligned. Data Security legislation has meant that while your Organization may not lose money through Data Loss itself, the financial penalties assign a fiscal loss as a result of poor controls. The outcome is that you're either paying a Governmental Organization, or a Fraudster!
In some ways it was inevitable that both Application Controls and Data Controls would collide and require these often different disciplines to work
together. These areas include Data Security, Application Security and IT and Business Users. In a recent project we conducted for GDPR compliance, we had
to look across Application access and the Data sources to establish what Data users had access to. This discovery process involved Functional, IT and
Information Security working together.
By evaluating the Access that users had we found weaknesses in the Application Controls that could have created audit findings,
openings for fraud and allowed access to data that was not in scope for the work these Users were undertaking. At the same time a review of all data at the source gave
the organization a complete picture of where PII was being stored and the ability to control that access and mask sensitive data.
In both Access and Data Security the key starting point is in the discovery, you cannot secure what you don't know exists:
* Where is all of our Sensitive Data?
* Have developers copied or created new columns that capture Sensitive Data?
* Which Applications have access to the Sensitive Data?
* Who has access to this Data within the Applications and how is granted?
Having this information allows you to understand what must be done and the policies that should be in place going forward to protect the Organization, it's Data and the Data of those who have been collected.
We are getting asked more and more "how can we secure both the Data and the Applications (and Users) accessing it?
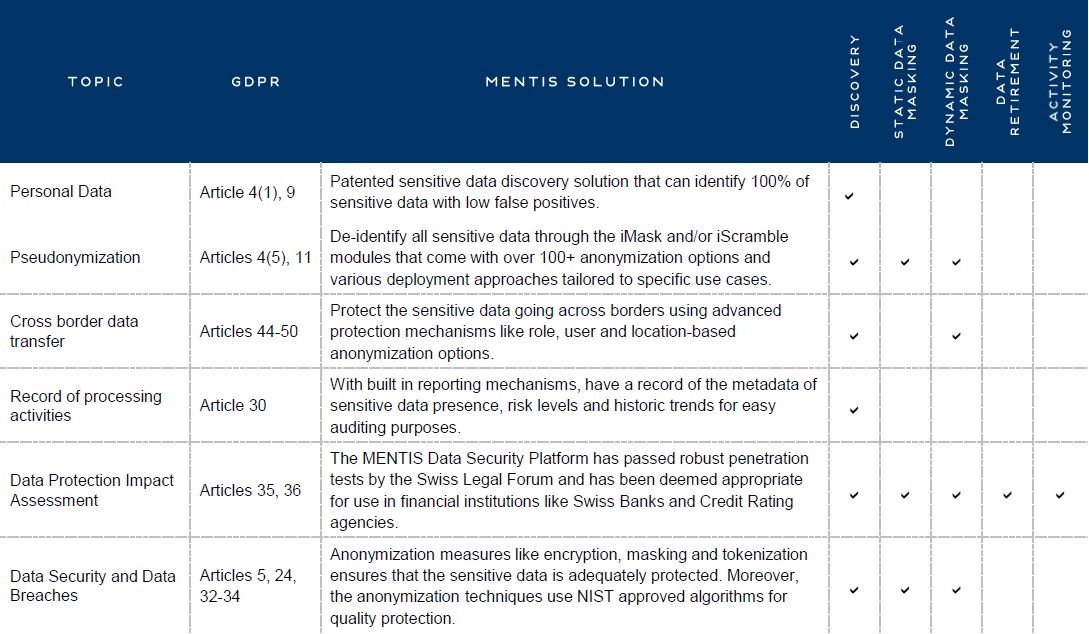
At Seecuring we have partnered with Mentis to provide a joint approach to securing both your Applications and the Data they inevitably access. From Data and Access Discovery (Sensitive Access and Segregation of Duties) through to remediation of Application Controls and Data Masking and other policies we are working to ensure that Organizations are able to meet both Audit, Data Protection and anti-loss/fraud goals.
Together we provide:
* Sensitive Access and Segregation of Duties Analysis within and across your Applications
* Sensitive Data Discovery across your Data Sources
* Data Masking and Data Policy Enforcement
* User Access Reviews and Remedial support
Once the discovery phase is complete, Seecuring and Mentis have the processes and technology to assist you through the remediation and ongoing management to satisfy Audit, Compliance and Information Security.
Our joint solutions will help save time, resources, and money - for the first time Data and Security Controls are aligned. Regardless of your Applications and Data stores we have you covered, from discovery, remediation and ongoing management.
Fraud and Data Loss - one and the same?
Securing the Financial Close